Via ST04 SQL commands, an administrator, or hacker can fire any SQL statement provided he has the authorizations.
Once the authorizations on S_DBCON are there, any SQL can be used to read and update any table.
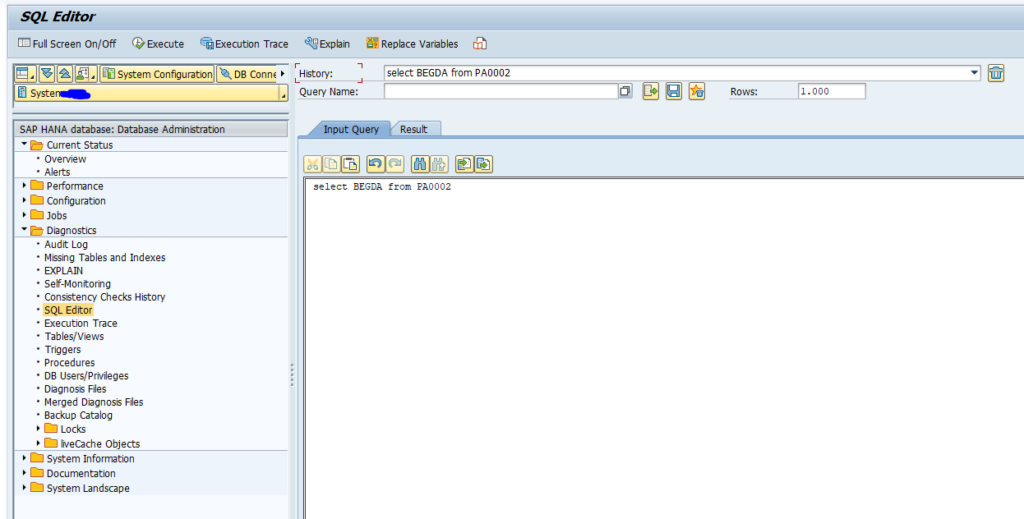
Firing SQL command via ST04
Start transaction ST04 and open the SQL editor in the Diagnostics section:
Now enter your SQL statement and press execute.
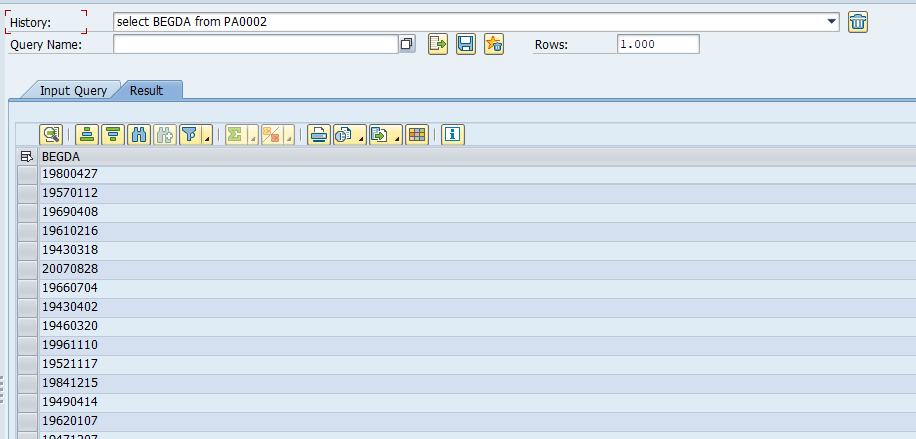
Result is shown:
How to avoid this?
If you don’t want people to use this function, withdraw the rights to do so. Authorization object S_DBCON is used to protect this.
Note that the SQL is fired using the SAP user of the system, not the ABAP user logged on.
Logging
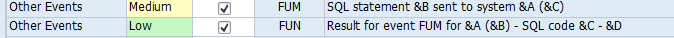
Logging is possible via the audit log. But this was only recently added. So it can be that either the events are not present, or that the events are present, but not yet activated.
OSS note 3331129 – DBA Cockpit: Logging of SQL Editor Commands in Security Audit Log or support package enables the logging function.
Make sure events FUM and FUN are switched on: