This blog series will explain the process of hacking SAP password hashes: also know as SAP password hacking. The process of hacking will be explained and appropriate countermeasures will be explained.
In this fourth blog we will continue with more complex attacks on the SAP password hashes and will also explain more preventive measures.
For the first blog on attacking the SAP BCODE hash click here.
For the second blog on attacking the SAP PASSCODE has click here.
For the third blog on attacking the SAP PWDSALTEDHASH has click here.
Questions that will be answered in this blog are:
- How does the rule based attack work?
- How to use the rules on found passwords?
- Where to find good rule books?
The rule based attack
The dictionary rule book attack is using the dictionary as input and then applies rules to the dictionary to generate a new password candidate.
Example words we will use are Password and Welcome.
Examples of apply some rules:
- Replace a with @ will give P@ssword
- Replace o with 0 will give Passw0rd and Welc0me
- Replace s with $ will give Pa$$word
- Replace l with ! will give We!come
- All rules above combined will give P@$$w0rd and We!c0me
For full list of possible rule syntax see Hashcat site on rule-based attack.
Suppose we have guessed one correct password for one user. He made the password Welcome1!.
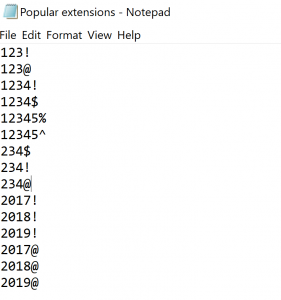
Now we will construct some rules:
- Replace e with 3, rule will be se3
- Replace l with 1 and l with !, rules will be sl1 and sl!
- Replace o with 0, rule will be so0
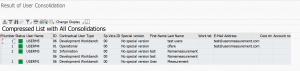
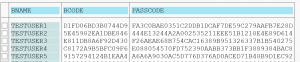
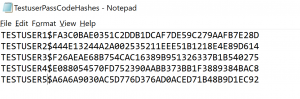
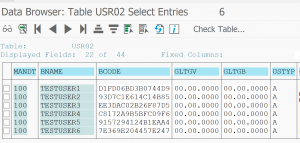
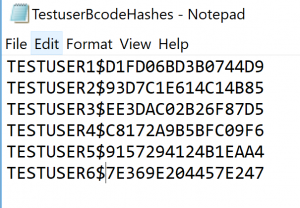
We use these 3 hashes as input:
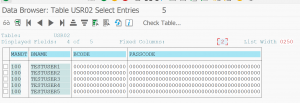
{x-issha, 1024}riqL3PXHJMOKkofOv1I4ObteIEGKw/OMny0U8MzMZ04=
{x-issha, 1024}7SC51LKZChMcpwmixb/ca/+qYvDxsXTbR3mE0IPrsaU=
{x-issha, 1024}AxErKhue0RAUveCTBgpAiJIaSDWGKdjpooiDSn5sTtg=
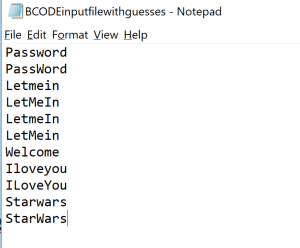
We construct an input file with word Welcome1! and a file with these rules:
se3
sl!
sl1
so0
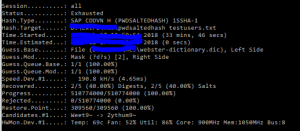
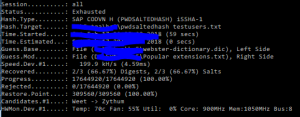
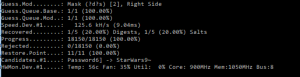
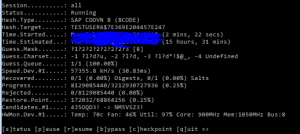
Now we call Hashcat with the rule based attack mode:
hashcat64 -a 0 -m 10300 -p : --session=all -o "C:\hashes_found.txt" --outfile-format=3 -n 32 --gpu-temp-abort=80 -r "C:\simplerules.txt" "C:\hashes.txt" "C:\welcome.txt"
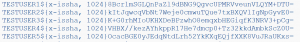
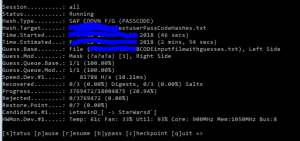
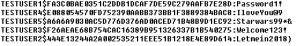
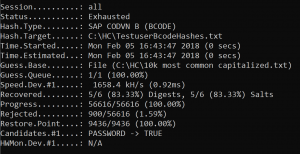
Great: 2 catches out of 3:
{x-issha, 1024}riqL3PXHJMOKkofOv1I4ObteIEGKw/OMny0U8MzMZ04=:We1come1!
{x-issha, 1024}AxErKhue0RAUveCTBgpAiJIaSDWGKdjpooiDSn5sTtg=:Welc0me1!
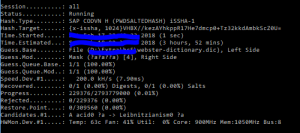
Now let’s add these rules:
o03
o13
o23
This means replace first character with digit 3, repeat for second and third.
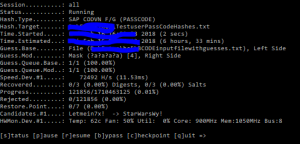
We run again Hashcat and find the 3rd one:
{x-issha, 1024}7SC51LKZChMcpwmixb/ca/+qYvDxsXTbR3mE0IPrsaU=:W3lcome1!
What has happened here? Why is this found now, and not before with the se3 rule, which should substitute the e with 3? Pretty simple: replace e with 3 in word Welcome1! will give W3lcom31!. So it replaces all and not first one. This is there background of having many rules.
Huge rulesets
With the Hashcat download you get a special directory called rules. Here there are some big rulesets available.
The nicest one is the RockYou list of rules. This is constructed based on the RockYou password list hacked in 2009 where 32 million passwords leaked. Based on English dictionary somebody has constructed the rules to come to most of these passwords.
Effectiveness of the attack
The effectiveness of the rule based attack is quite high. If you have found 1 password, you just run the complete ruleset of one of the huge lists to find multiple variations. People are not so inventive and creative. You will be surprised on the amount of password variations you find on the following words:
- Welcome
- Summer
- Winter
- Password
- Apple
- Android
Hackers don’t start with the full dictionary. They start with the top 1000 words and apply many rules to them. From the passwords found they will start to derive patterns of the users. Any new password is processed through many new rules to generate candidates with higher potential.
The name and or abbreviation of a company is word number 1 to add to the favorite word list.
Further optimization of the attack speed
For optimizing the attack speed, read the fifth blog on SAP password hash hacking here.
Prevention measure 1: frequent change and large change per time
Many companies have implemented a more faster cycle of password changes. In the past once per year was common. Nowadays 60 to 90 days is more common practice. Set this in profile parameter: login/password_expiration_time.
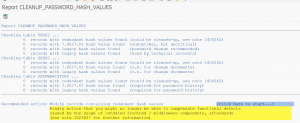
More important is to make a larger change per time the password changes. This is to avoid the rule-attacks explained above to become very effective. How many people just simply change and increase single digit in password? Or increase the special with the next one on the keyboard. Set the profile parameter login/min_password_diff to sufficiently high value of 3 or more.
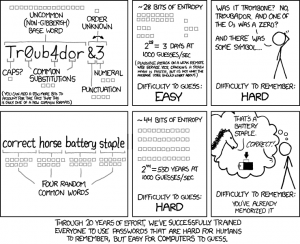
Prevention measure 2: length
Explain to your users that length is more important than complexity by using this famous explanation:
Prevention measure 3: stronger hashes
Stronger hashes simply take more time to crack. To set stronger hashes, read this dedicated blog.
Next blog on password hacking
The fifth blog on password hacking is about optimizing the attack speed. Read on in the blog. And the blog on extended word lists.