Information disclosure is a potential security risk. Most IT software has a way to show the exact software version. This detailed information can be useful for an end user submitting an incident. Or for an administrator to know if certain patching is needed for an IT system.
But the detailed version information can also be used by a hacker to know if the system is vulnerable for some known attacks (and the system is not yet patches with the fix).
Hence for IT systems one should be careful and conscious about showing detailed version information: this is called information disclosure.
Known information disclosure items
ABAP System / Status
In ABAP stack, you can reduce the information in System/Status via authorizations. See OSS note 2658772 – System -> Status: Restriction of the available information.
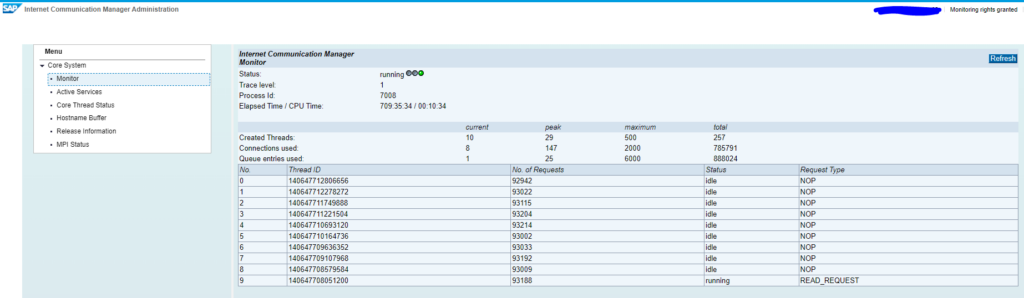
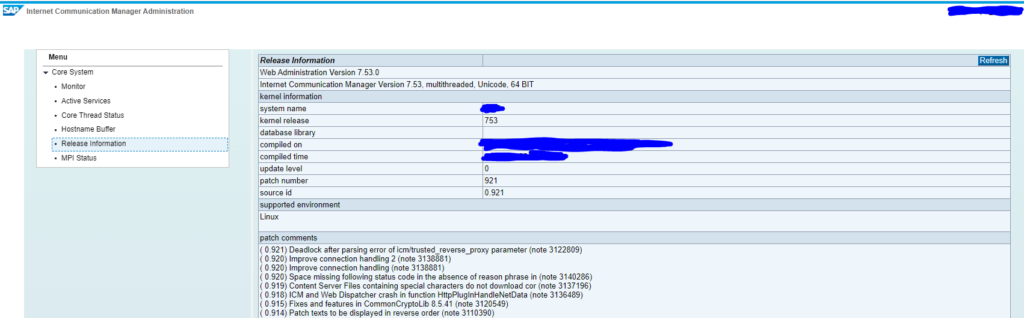
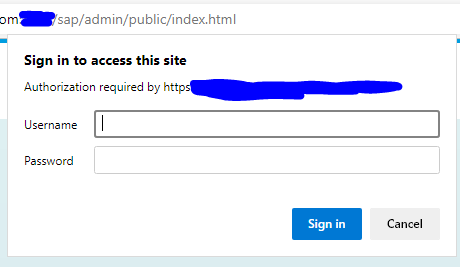
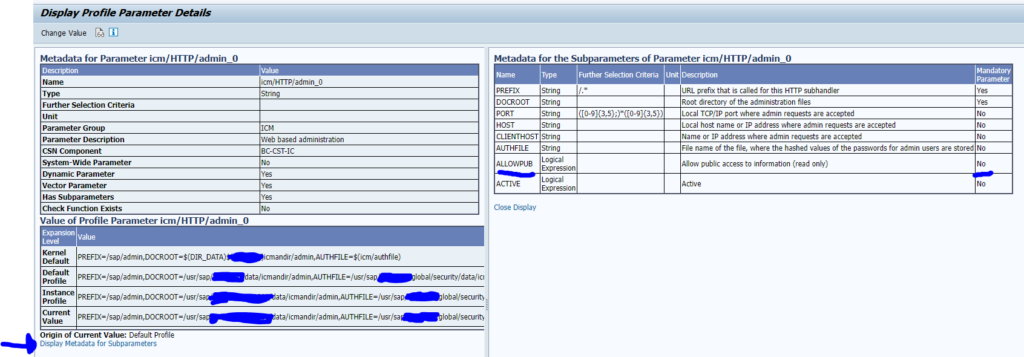
Web administration interface
The web administration interface is a very known one. How to solve, read this blog.
Information disclosure security notes
Every month SAP release security notes (see blog). For the SAP systems that are internet facing (like portals, Netweaver Gateways, PI systems), check and apply the information disclosure notes as soon as possible. For the other systems, apply them at your normal security cycle speed.